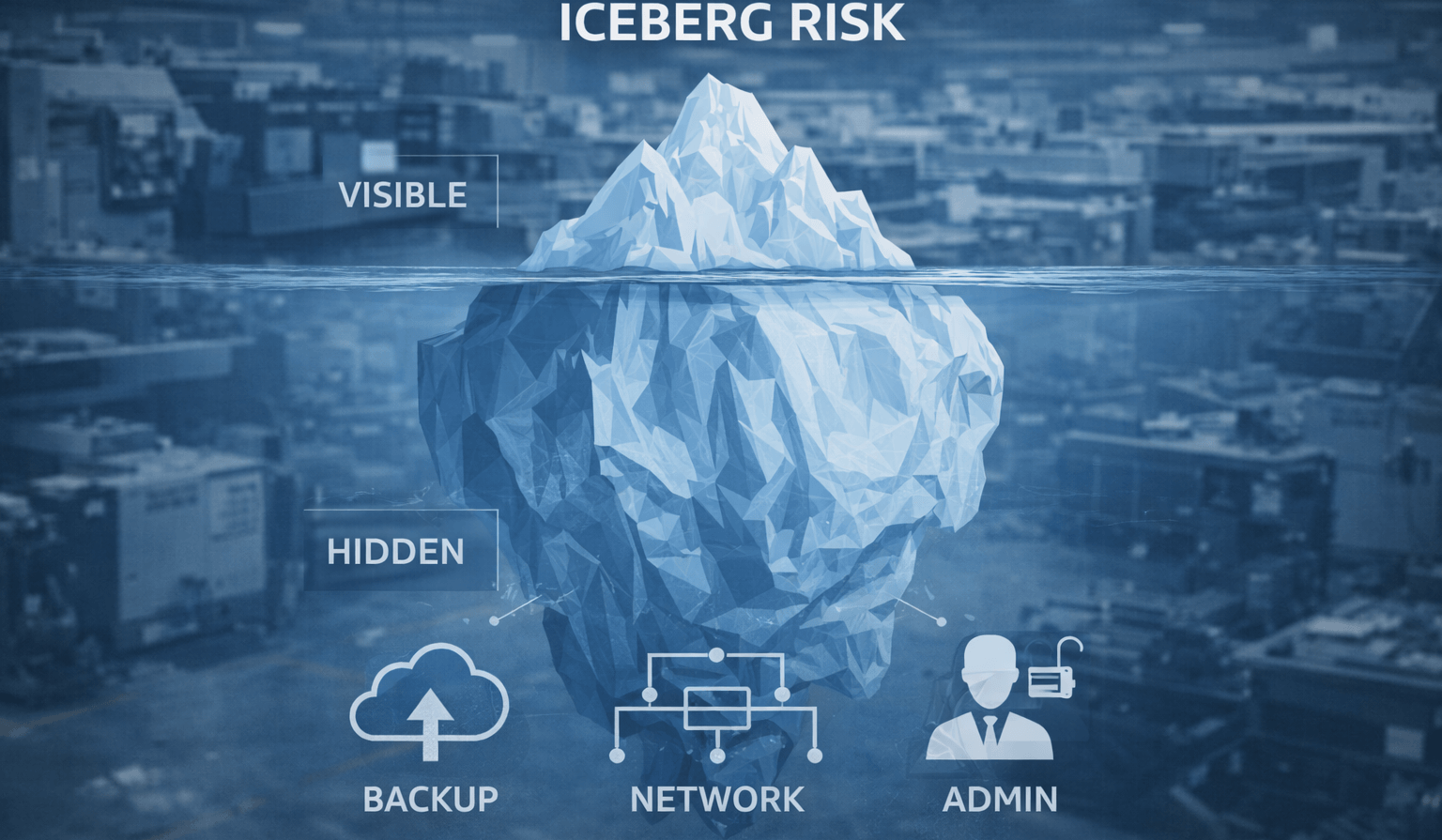
The biggest IT risks in manufacturing often look “fine” until they cause a shutdown. Untested backups, aging network gear, over-permissioned CAD shares, unmanaged admin accounts, flat networks, and no IT roadmap are common in 20–100 employee manufacturers—creating outsized executive exposure because they turn small incidents into multi-day downtime or ransomware events.
Why “Everything Works” Is Not the Same as “We’re Safe”
Manufacturing IT often runs on stability habits:
- “Don’t touch it, it might break”
- “We’ll patch later”
- “Backups are running”
Hidden risk is what looks normal, until the day you need recovery.
The Hidden Risk Framework (7 Categories)
- Backups That Don’t Restore
- No restore testing schedule
- No immutable/offsite copy
- Aging Network Infrastructure
- Old switches/firewalls
- No redundancy
- Random outages and slowdowns
- CAD/Engineering Data Overexposure
- Broad permissions
- Shared accounts
- No monitoring for mass file changes
- Admin Account Chaos
- Shared admin credentials
- No MFA for admin actions
- Old vendor accounts still active
- Flat Networks
- Office infection spreads to servers/production
- No containment boundaries
- Patch Delays / Unsupported Systems
- Legacy OS in production
- Unpatched perimeter devices
- No IT Roadmap
- Reactive spending
- Surprise failures
- No lifecycle planning
The 10-Min Executive Test (Quick Self-Assessment)
If you can’t answer these with evidence, risk is high:
- When was our last restore test?
- What’s our ERP RTO/RPO?
- Do we segment office vs production?
- Do admins have MFA + separate accounts?
- What systems are end-of-life?
Illustrative Scenario: Hidden Risks That Looked “Fine” Until They Didn’t
A 55-employee apparel manufacturer had stable day-to-day operations, but backups were untested and key network gear was aging. Everything seemed fine, until an outage revealed how fragile recovery really was.
After a structured program:
- Monthly restore spot checks and quarterly restore tests were implemented
- Admin accounts were cleaned up and MFA enforced
- High-risk network components were prioritized for replacement
- A phased roadmap aligned upgrades and resilience improvements
Result: fewer unplanned incidents and more confidence in recovery when disruptions occur.
Trust Signals
- Restore testing + documentation
- Admin controls + MFA enforcement
- Segmentation for production environments
- Roadmap planning that avoids disruption
Find the Hidden Risks Before They Become Downtime
Hidden risks are the ones that look normal, until they cause a shutdown. A quick scan helps leadership focus on the few items that create the biggest exposure.
Book a 30-minute call with Fothion today and we’ll:
- identify your top 5 hidden risks (backups, admin access, CAD permissions, aging gear, flat networks)
- rank them by downtime and ransomware impact
- recommend the fastest fixes and roadmap priorities to reduce exposure
